Alternative technology, or ‘alt-tech,” social networks have soared in popularity. But that growth has, unfortunately, also drawn scores of criminals and extremists.
It also means trouble for security teams.
With users splintered across so many sites, it’s harder than ever to keep an eye on everything. If a threat actor posts something on a new social network, it might slip past you undetected.
Your security teams could get caught flat footed by an incident you later discover was announced for everyone to see online.
It didn’t crop up out of the blue. You just may not have line of sight to it.
For proof, consider the January riots in the U.S. Capitol. Ahead of President Biden’s inauguration, some commentators noted a rise in extremist rhetoric on alt-tech social networks. But because posts occurred off mainstream websites, some security teams failed to take action.
So how can you keep up? Analysts must spot and monitor new alt-tech social networks.
Easier said than done, of course.
New websites pop up all the time. And once hot services, like Voat and Parler, can go offline overnight.
But monitoring new social networks can represent a valuable source of threat intelligence. And failing to do so could leave gaps in your security program.
So, now you know why these websites are important. Let’s next break down the top alt-tech social networks to watch in 2021.
1. Gab
Gab is an alt-tech website that bills itself as the “free speech social network.”
Its interface looks like a mix between Facebook and Twitter. Users can post messages, called “gabs,” of up to 300 characters. But unlike other social media sites, Gab enforces minimal oversight over content.
Such a hands-off approach to content moderation has created controversy.
Gab first made headlines in 2018. Before staging a mass shooting at a Pittsburgh synagogue, gunman Robert Bowers used the network to post anti-semitic content. Today, the site also serves as an influential hub for QAnon followers and right-wing extremists.
And that influence will likely grow in 2021. After Amazon suspended web hosting services to rival Parler in January, hundreds of thousands of people have migrated to Gab. That growth should continue as mainstream social networks ban controversial users from their sites.

Gab has also released its own web browser, Dissenter.
In addition to browser capabilities, Dissenter creates an unmoderated discussion forum for every web page online. This enables users to leave comments on news articles, blog posts, Wikipedia pages, or even individual tweets.
For the Dissenter community, this allows for real-time conversations between members. Such conversations, however, are invisible to regular internet users.
2. Telegram
WhatsApp has long ranked as the world’s number one messaging app. But in January, the company said it will start sharing users’ data with Facebook.
That decision drew the ire of privacy advocates. It also sent some users scrambling to find an alternative service.
One big winner from the exodus: Telegram.
Telegram provides users end-to-end encrypted communications. In addition, the app also offers public and private channels where members can broadcast messages to followers. Those features have allowed Telegram to grow to more than 500 million active users worldwide.
Strict privacy features, however, make Telegram a convenient place for extremists. Fringe groups, including neo-Nazis, white supremacists, and QAnon followers, have rushed to sign up.
To Telegram’s credit, executives have taken action against such content. In January, the company banned 15 extremists channels. Management has also blocked content from users calling for violence.
Regardless, Telegram’s fast-growing user base will make it an important alt-tech website through 2021 and beyond.
3. BitChute
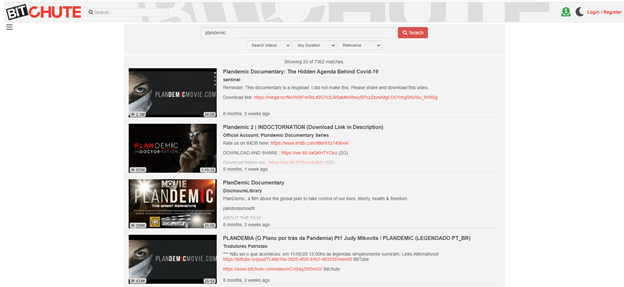 British web developer Ray Vahey launched BitChute in 2017. The company markets itself as a peer-to-peer service. In other words, BitChute doesn’t actually host content itself. Rather, it simply helps transferring videos between users.
British web developer Ray Vahey launched BitChute in 2017. The company markets itself as a peer-to-peer service. In other words, BitChute doesn’t actually host content itself. Rather, it simply helps transferring videos between users.
The site’s primary selling point, however, is as a YouTube alternative. And much of the BitChute community consists of fringe political groups banned from other platforms.
Conspiracy theory channel InfoWars switched to BitChute after getting kicked off YouTube. The site also hosts a number of controversial commentators including Lauren Southern, Stefan Molyneux, and Paul Joseph Watson.
The biggest concern BitChute represents for security professionals comes down to harmful viral content.
The platform lists large amounts of misinformation related to healthcare products. Most notably, Bitchute continues to host the viral conspiracy theory video “Plandemic” long after other platforms had removed it.
4. Discord
Discord ranks as one of the world’s fastest-growing gaming apps.
Users can communicate with friends in private chats. Alternatively, the site also hosts conversations for wider communities in groups called “servers.”
You could almost think of it as Slack for gamers. Though in recent years, management has started marketing the site to a wider audience.
Those efforts to diversify, however, have attracted some less than savory characters.
Discord’s privacy features make it the perfect set-up for cybercriminals. The app’s private groups can serve like retail stores. And inside, visitors can buy illegal products like hacked customer accounts and stolen credit card numbers.
Moreover, Discord has become a refuge for the darknet chan board 8kun. The controversial online forum, which journalists have linked to multiple mass-shootings, has struggled to secure cybersecurity protection services. So as a result, 8kun users have switched to private Discord communities.
5. 4Chan
4chan is an anonymous imageboard based on sharing of pictures alongside text and discussion.
The site has developed a bad reputation due to its links to hacktivists and the alt-right. But for the most part, 4Chan serves as a hub for many topics such as anime, memes, politics, and others.
Still, 4Chan can represent a useful source of threat intelligence.
In the past, terrorists and mass shooters have posted their manifestos on the website. Discussions around these incidents can allow analysts to spot threats and mitigate risks.
Furthermore, lone actors and activist groups have used 4Chan to organize campaigns against businesses. For example, users may uncover and share personal details about an executive. Members have also used 4Chan to leak intellectual property.
In mid-2020, for instance, an anonymous 4Chan user leaked over two terabytes of stolen Nintendo source code and internal communications.
The leak also contained documentation on the company’s development projects. All of which could, in theory, allow criminals to create illegal copies of Nintendo hardware.

The Bottom Line on Alt-Tech Social Networks
Bad actors still want their message to reach the most people. For that reason, you can likely identify most threats against your organization by watching the biggest platforms.
But mainstream services continue to bar fringe groups from their communities. And as result, these users will migrate to new sites for recruitment, communications, and planning.
If you want to keep up with an evolving threat landscape, your security team must spot and monitor new alt-tech social networks as they grow and develop.
