If you’re an event security professional, then you have a lot on your plate.
Teams have to spot and manage all kinds of different risks. That could include everything from trespassers and theft to gunmen and weather.
Moreover, personnel now deal with more digital headaches, too.
Bad actors might post threats on Gab. An onlooker could leak a VIP’s location on Twitter.
So how can your event security team shore up defenses?
To safeguard their venues, more organizations have started to watch social media.
To be fair, these sites remain mostly in the domain of marketing departments. In most cases, businesses use social platforms to promote events and engage with fans.
But that has started to change. More and more, social media tools have a place in the security operations center.
Teams have discovered these platforms present a powerful way to spot threats. Or in the event of a crisis, they’re critical for attaining situational awareness.
Let’s take a look at a few social media use cases to keep staff, attendees, and property safe.
Anticipate Threats
Effective event security often comes down to planning. Teams must predict what types of threats could arise. Then they have to spread their resources accordingly. Social media monitoring can play a key role in this process.
The NFL’s Minnesota Vikings provide a case in point.
In 2013, the team played its final home game at the Metrodome Stadium. But ahead of the event, online chatter hinted some fans had planned a postgame field rush. And this didn’t represent some remote possibility, either.
In 1981, fans rushed the field after the team played their final game at the old Metropolitan Stadium. They looted anything the venue didn’t have bolted down beforehand.
“[Social media monitoring] allowed us to have an idea of what was going on in the mindset of people in the building,” director Jeff Spoerndle told the Associated Press.
In response, the Vikings added more security guards fieldside ahead of the game.
That thwarted fans’ efforts to disrupt the event. And it ensured a safe evening for everyone.
Maintain Situational Awareness
Picture yourself as head of security for a large event with thousands of attendees.
You don’t have enough people to have eyes everywhere. So it’s easy to imagine any number of scenarios that play out before your team can notice:
- A fight breaks out
- An attendee leaks the location of a VIP
- Someone leaves a bag unattended
These don’t present a big security risk… yet.
Still, they could escalate quickly. And once you have an incident underway, it can be tough to regain control.
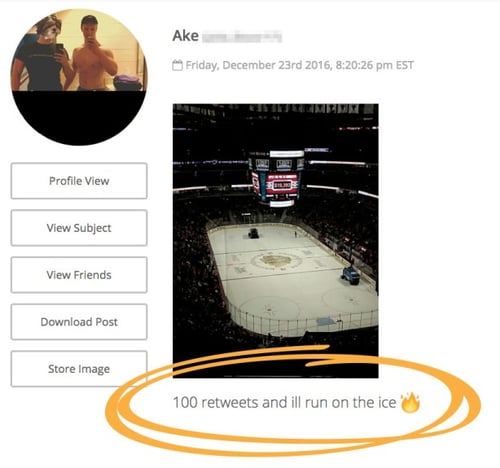
A fan discussing plans to disrupt an event on social media, discovered by Navigator.
Often, however, incidents pop up first on social media. And if an analyst spots something suspicious online, they can alert one of your team members.
For instance, you can send security guards to settle down rowdy fans.
You could escort a VIP to a safer location.
Or you might send a team to check out an unattended package.
In each case, you can investigate threats before they escalate into a serious incident.
Pinpoint the Location of Threats
Marking a perimeter around your venue is often the first step in effective event security. You need to see everything that happens inside that space. And you need to be able to act within that area.
Geofences can help during this process.
Simply put, a geofence represents a virtual perimeter around a real-world geographic area. This allows your team to spot social media posts from inside these boundaries. And once outlined, staff can watch out for content that presents a security risk.
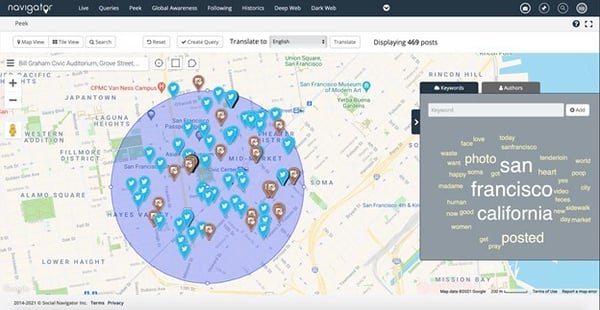 A geofence perimeter watching social media activity around the San Francisco Bill Graham Civic Auditorium, created by Navigator.
A geofence perimeter watching social media activity around the San Francisco Bill Graham Civic Auditorium, created by Navigator.
To be clear, this technique won’t map all content posted to social media.
It will only locate posts by users that have enabled geotagging. So as a best practice, be sure to create a geofence alongside keyword queries as well.
Still, geofencing serves as a powerful tool for security teams.
Figuring out where threats originate from is tough at large venues, like stadiums or convention centers. But place-based data allows staff to locate issues quickly.
Prevent Data Leaks
One of the biggest sources of data leaks? Big events.
Your marketing team has spent months building anticipation for an upcoming announcement.
Or your CEO has created a presentation for the company’s next product launch.
It only takes one onlooker posting a clip to YouTube to spoil everything.
Data leaks present a physical security risk, too.
For instance, an employee might upload an image of their ID badge to social media. Excited fans often post pictures of their tickets online.
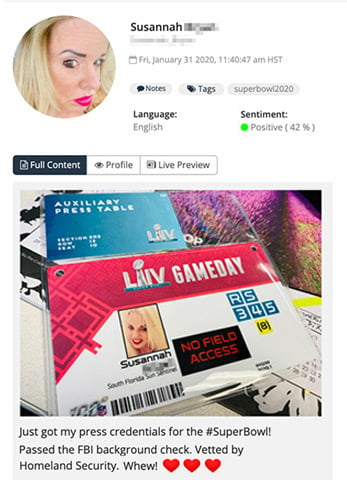 A journalist posting an image of their press credentials to social media, discovered by Navigator.
A journalist posting an image of their press credentials to social media, discovered by Navigator.
Insider data leaks represent juicy information for criminals. With an image of an ID badge, for instance, it’s easy to print a replica. That could let trespassers get into secured areas.
The same applies to pictures of tickets. With a photo to work from, it’s not hard for criminals to produce fakes. And they don’t need a perfect fake, mind you.
Counterfeits just need to be good enough to convince busy staff. Or trick a fan looking to score a deal on seats.
Communicate With Attendees
Finally, social media also presents a useful method for communicating with attendees.
As a best practice, use hashtags to organize your content (i.e. #BellCentre or #ComicCon2021). Tell attendees to watch this tag and use it for their own posts.
Obviously, this represents a great tactic to engage with fans. But it also makes it easier to distribute information.
Event staff could announce venue changes, such as parking restrictions or closed entrances. It’s also useful for reporting security, weather, or other emergency issues.
The Bottom Line
Admittedly, social media doesn’t represent a silver bullet for event security. But it can serve as a useful addition to your team’s toolkit.
A single analyst online can be enormously effective at spotting threats. That can stop small incidents from becoming a bigger issue. And that can go a long way towards keeping everyone safe.
Of course, this post only scratches the surface of this topic.
Interested in learning more about protecting your company’s personnel and property? We publish useful tips every Tuesday.
Get our best insights every week by entering your email address into the box below.
