Oftentimes internet security-related topics can be difficult to understand.
Conversely, a picture says a thousand words! So we are hoping to bridge that gap using everyone’s new favorite method of communication – memes. We have chosen some of our favorites to explain where on the web your data may end up and how (if you aren’t careful) it got there.
Below surface
The deep web is web content that you can find on the internet but that isn’t indexed via a search engine – which makes it difficult to search for and find manually. Deep web often includes content that could be poorly indexed, ie page 50 on google.
Example: Comments and posts on forums, posts on Classifieds, Paste Sites.
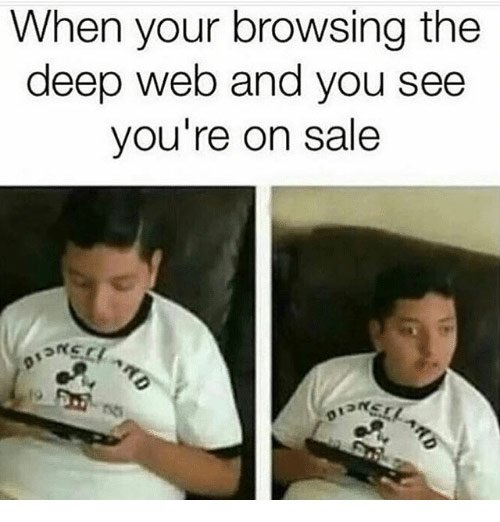 On the deep and dark web you can find personal information such as credit card numbers, emails, passwords, and social security numbers.
On the deep and dark web you can find personal information such as credit card numbers, emails, passwords, and social security numbers.
It’s not all dark
The darknet or dark web is a completely separate network on the internet from the world wide web (www). The darknet is only accessible by means of special software. The content on this network cannot be traditionally indexed by a search engine, which is how most of us “search” on the internet as we know it (unless you have access to software like Navigator). Identities are masked on the dark web by its VPN structure – which makes users anonymous, thereby making it appealing for its renowned criminal activities.
Example: TOR, FTP, 12P
 Commonly, the dark web is an environment in which criminal activities are discussed or take place, however other examples include workplace chatter, whistleblowing, and like-minded groups/causes.
Commonly, the dark web is an environment in which criminal activities are discussed or take place, however other examples include workplace chatter, whistleblowing, and like-minded groups/causes.
Avoid the bait
Phishing is an illicit attempt to acquire personal information such as passwords and credit card information. This occurs when the attacker acts as a trusted or reputable source in an attempt that the entity will disclose valuable or personal details.
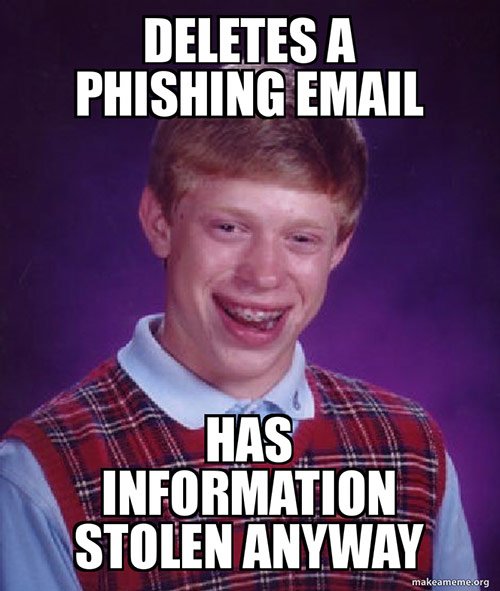 Phishing transpires when an individual opens a disguised email or message that either contains malware or directs you to a link that requires you to input additional information.
Phishing transpires when an individual opens a disguised email or message that either contains malware or directs you to a link that requires you to input additional information.
Don’t be predictable
Passwords are the codes that allow you to secure your entity, requiring permission to gain access. They are crucial for maintaining privacy and overall personal security.
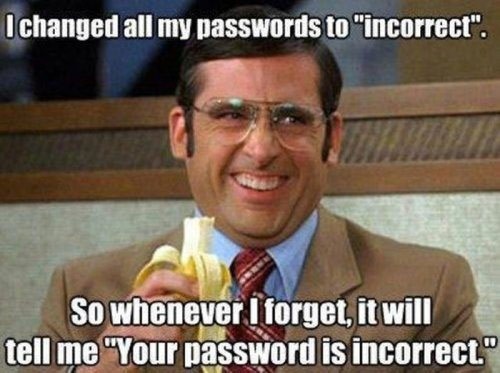 Passwords longer in length that include a variety of characters are better in strength and are harder to reveal to hacker.
Passwords longer in length that include a variety of characters are better in strength and are harder to reveal to hacker.
Don’t be fooled – It’s not sugar-coated
Scams are a fraudulent action often intended to trick individuals into providing sums of money or disclosing personal information.

“I didn’t say it, I declared it” – Michael Scott
Data breaches arise when confidential, private, or sensitive personal information is leaked to the external public (often online nowadays).
 Large organizations have become huge targets for breaches as their records contain a mass of undisclosed data.
Large organizations have become huge targets for breaches as their records contain a mass of undisclosed data.
All jokes aside, being aware of the potential issues that can occur with your data is a helpful first step in avoiding privacy exploitation. However futile it may seem in these digital times, the more you can do the protect yourself, the better.
