As a security professional, you have a lot on your plate. Teams must defend a growing number of assets: worksites, customers, employees, infrastructure, supply chains, intellectual property.
International expansions also mean security leaders must keep tabs on risks and threats worldwide. And failure to do so can be costly, from hefty fines and damage to extended business disruptions.
To get an edge, your security strategy must be intelligence-led. Resilience relies on proactively anticipating threats rather than responding after the fact. And as the amount of data available grows each year, this creates new opportunities for savvy security professionals.
One data source analysts shouldn't overlook is the vast amount of public information uploaded to social media. Every minute, users publish terabytes of content. And wherever you find like-minded people congregating, the risk of nefarious behavior grows.
That has created the need for social media intelligence (SOCMINT) and SOCMINT platforms.
What is SOCMINT?
Social media intelligence, or SOCMINT, is a sub-discipline of open source intelligence.
Simply put, SOCMINT refers to the collection and analysis of data gathered from social media to produce actionable insights for decision-makers. And while historically used by some national security and law enforcement agencies, SOCMINT has started to play a growing role in corporate security functions as well.
When discussing SOCMINT, most people tend to refer to the gathering of intelligence strictly from social networking sites like Facebook and LinkedIn. This isn’t wrong, but it doesn’t provide the full picture of the type of data sources analysts can exploit.
In addition to social networking sites, SOCMINT researchers also mine information from other online communities such as:
|
Video sharing |
Websites dedicated to sharing recorded and live video broadcasts. YouTube ranks as the most popular of such platforms on the web. But you can find other notable services such as Rumble, Bitchute, and Dailymotion. |
|
Photo sharing |
Websites used to upload, store, and share photos, which are made available to connections via a personal page. Popular examples include Instagram and Flickr. |
|
Review sites |
These platforms allow users to write reviews for employers they have worked for or products they have purchased. Examples include sites like Yelp, Glassdoor, and Angie’s List. |
|
Social bookmarking |
These websites function in much the same way as your web browser’s bookmark folder. But in addition to keeping tabs on content discovered online, social bookmarking sites allow users to share their discoveries with others through added tags and annotations. Atavi and Pinterest are examples of sites that fit into this category. |
|
Social gaming |
Social gaming sites have exploded in popularity. These platforms allow users to play games with people from around the world or live stream their sessions to others. Popular examples include Steam, Twitch, and Xbox Live. |
|
Forums |
Forums represent one of the first types of online social media platforms. These simple communities provide a place for users to share ideas on topics in the form of posted messages and replies. Reddit is probably the most well-known example. But you can find thousands of communities catering to niche interests across the web. |
|
Microblogs |
Microblogging platforms allow users to publish short blog posts designed for quick, direct audience interactions. Examples include Gab, Parler, and Mastodon. |
|
Chanboards |
Occasionally referred to as image boards, chan boards are anonymous forums that exist on both the surface and dark web. On these sites, users can share images and discuss common topics of interest. Popular examples include 2Chan, 4Chan, and 8kun. |
|
Blogs |
An online journal where an individual or organization presents a record of thoughts, activities, or opinions. WordPress ranks as the most popular blogging platform on the web. |
Social Media Intelligence is Essential to Organizations for the Following Reasons:
Real-Time Threat Intelligence
SOCMINT’s primary benefit is the fact that it provides real-time threat intelligence. Violent threats often pop up first online. Increasingly, CSOs have started to pay attention to what’s happening on Instagram, Facebook, and Reddit. Events often get reported first on these platforms. Sometimes hours before a story hits mainstream news outlets.
By watching these channels, teams can respond faster to events.
In quite a few scenarios, these efforts have paid dividends.
A prime example of the benefit of this kind of real-time intelligence occurred in 2021 when a political extremist posted his plans to bomb an Amazon data center online. Company officials alerted law enforcement of the imminent threat, preventing an attack and saving lives.
Cost-Effectiveness
By capitalizing on social media users’ existing digital footprint, SOCMINT provides organizations with a cost-effective solution for identifying potential security risks. Through social media monitoring tools and publicly accessible data, businesses can gain invaluable insight without investing in expensive technology or services.
Identify Threat Locations
Posted online images are an invaluable resource to security professionals. The data embedded in these photos, known as metadata or EXIF data, offers insight into a shot's camera settings and geolocation. The applications of this intelligence are numerous. Analysts can use this threat intelligence to pinpoint the location of a threat actor or emerging hazard. It can also assist with more proactive travel and route planning.
Prevent Data Leaks
A data leak's financial consequences can be devastating. From revenue loss to reputation damage, the potential costs are staggering.
SOCMINT enables security teams to scour the depths of social media, fringe online communities, and dark web marketplaces where bad actors trade leaked data.
How SOCMINT Supports Security Teams
Security and intelligence teams employ SOCMINT to identify risks, monitor emerging hazards, and validate potential threats. That can have applications for organizations on both the strategic and tactical level.
At the tactical level, SOCMINT can provide almost instantaneous information about what’s happening on the ground in a particular location. Information, it’s worth emphasizing, that local media outlets often cannot deliver. That can have a swath of applications from loss prevention and IP protection to event and travel security.
For example, analysts may identify the location of a threat actor by extracting EXIF data from a series of posts. They could then send that information to a protection team to assist with travel and route planning for a high-profile individual.
Additionally, SOCMINT can also identify information threat actors might use to attack your business. Pictures posted online by friends or family members, for instance, could reveal the home residence of a key executive. Alternatively, bad actors can exploit employee information posted online in social engineering schemes or access secured facilities.
To say that social media intelligence is a crucial part of any corporate security strategy is an understatement. Nowadays, threat actors feel comfortable sharing their intention to commit violent or malicious acts online. By leveraging SOCMINT to monitor emerging threats, businesses can avert and respond to malicious activity before it causes irreparable harm.
This intelligence can allow security teams to see public information about their operations. With that information on hand, they can then find ways to mitigate any vulnerabilities.
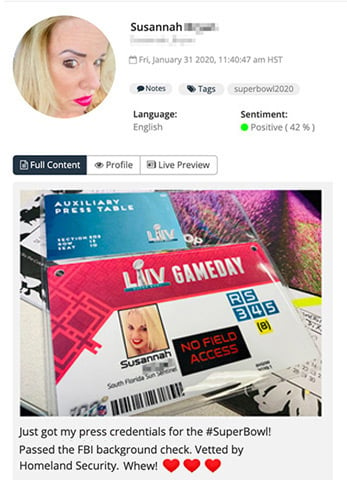 A journalist posting an image of their press credentials to social media, discovered by Navigator. Threat actors can exploit such photos to gain unauthorized access to secured facilities.
A journalist posting an image of their press credentials to social media, discovered by Navigator. Threat actors can exploit such photos to gain unauthorized access to secured facilities.
At the strategic level, SOCMINT can provide forward-looking insights for executives. Security leaders, for starters, exploit social media intelligence for information and warnings about developing threats. That can help high-level personnel make better decisions when it comes to staffing, resource allocation, or other priorities.
SOCMINT can provide insights for other stakeholders too. Today, social media represents the go-to place for taking a pulse on public opinion. Whether your company wants to understand public perception for business expansion or respond appropriately to a PR crisis, SOCMINT research can help executives make better-informed decisions.
In the world of corporate security having all the answers is not as important as knowing
where to look for them.
Challenges for SOCMINT Analysts
Social media intelligence can provide actionable insights for executives and security personnel. But as a new discipline, SOCMINT analysts face numerous challenges.
For example:
- Data Overload: Users upload far more content to the web than any individual could possibly comb through and analyze. So to glean useful intelligence, teams must employ sophisticated tools to automate data collection and analysis.
- Fake Profiles and Bots: It’s no secret that bots represent a growing problem on social media. And as artificial intelligence improves, spotting fake accounts becomes even more challenging. That makes it tough to separate fact from fiction online.
- Public Relations: The line between public and private information isn’t always clear-cut. Additionally, lawmakers have introduced new legislation, such as GDPR rules in Europe, to protect consumer privacy. As a result, conducting any social media intelligence can expose organizations to legal risks or backlash from the public.
- Obscure Communities: Most people already have a handle on mainstream social media sites, like Facebook, Instagram, and Reddit. But many security teams overlook new, more obscure alt-tech communities online. That could result in analysts missing key threats to their organization.
To address these challenges, intelligence teams increasingly rely on SOCMINT tools and technologies. These tools vary in price and functionality. But they’re needed to turn the sheer volume of data published online into insights for security teams at scale.
The Bottom Line on Social Media Intelligence
Evolving threats to organizations require a predictive, intelligence-led strategy. To anticipate risks, security leaders must gather information from everywhere they can. And social media intelligence represents an increasingly important tool to inform decision-makers.
Not only can SOCMINT help protect against attacks such as theft, fraud, or violence. It can also provide teams with real-time, location-based situational awareness to respond faster during crisis situations.
All of which can give your team an upper hand.
Reach out to us for a custom-made solution that allows you to benefit from the advantages of modern technology while keeping safety at the forefront of operations.
|
5 OSINT Investigation Mistakes You Don’t Know You’re Making We’re all ‘hard wired’ with cognitive biases to simplify complex decisions. But these mental heuristics can lead to faulty analysis, sabotaging OSINT investigations. In our free guide, we list the five most common cognitive biases that plague open-source analysts and outline practical strategies for how to deal with them. |
 |
