The internet has allowed close protection teams to access vast swaths of information with the click of a mouse. Unfortunately, that is also true for those looking to harm a VIP or executive.
Twenty years ago, a stalker would have a tough time obtaining the travel plans of their target. Today, social media makes it easy to track any individual online.
Moreover, globalization means executives travel more than ever. And oftentimes, this involves visiting unstable regions where conditions on the ground can change overnight.
So how do close protection teams adapt to this new reality?
Increasingly, details have turned to open-source intelligence, or OSINT, to keep VIPs and executives safe.
By accessing the right information at the right time, details can improve situational awareness, proactively spot threats, and respond to incidents faster.
Still, most security leaders fail to exploit OSINT to its full potential. And many organizations don’t consider a potential use case until after an incident occurs.
Which begs the question, “How can organizations fully exploit OSINT for close protection?”
Let’s look at why open-source intelligence has started to play a bigger role in the world of physical security and some practical applications for these techniques.
Learn More: 5 Cognitive Biases That Could Affect Your OSINT Investigations
The Future of Close Protection
A polarized political climate has turned the web into a dangerous place for high-profile individuals. And by extension, this has also created more headaches for close protection teams.
For starters, the public increasingly demands CEOs and celebrities express their perspective on controversial political topics.
No longer can VIPs stay anonymous on the sidelines. Yet the moment they express an opinion, principals can anger millions of people and immediately paint a target on their back.
With countries becoming more polarized politically, someone always escalates a conflict too far. And increasingly, we’ve seen attackers exploit personal information to dox, phish, impersonate, or threaten their targets.
Would-be attackers have no difficulty uncovering such personal information, either.
In recent years, media outlets have published alarming stories on the Dark Web, which refers to a network of encrypted websites unindexed by normal search engines. Here criminal outfits buy and sell personal data such as usernames, passwords, bank information, and more.
But in our experience at Liferaft, bad actors uncover most of the data they need for attacks right out in the open on the surface web.
Today, anyone with an internet connection can uncover a principal’s basic personal information.
And it only takes minimal research skills to uncover more sensitive data, such as confidential personal addresses, upcoming travel plans, and the names of family members.
Making matters more complicated, most executives no longer work from the protective confines of the office.
Previously, teams could keep a principal safe behind a secured entrance, video monitoring, and trained guards. But today, executives are far more likely to work from their personal residences over unsecured networks.
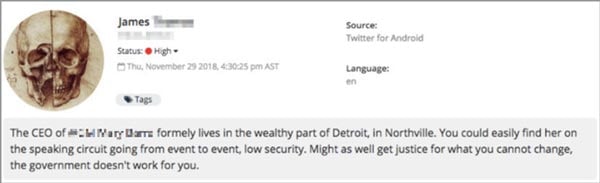 A threatening post directed towards a senior executive, discovered by Navigator.
A threatening post directed towards a senior executive, discovered by Navigator.
Against this new backdrop, close protection teams must now be intelligence-led.
It’s not enough to be the bodyguard waiting to stop bad actors. The growing number of threats and attack avenues means most details struggle to acquire enough resources to keep principals safe.
Instead, protectors must stretch their limited budgets by taking a more proactive stance. This means predicting, preventing, and preparing for attacks/issues before they occur.
Moreover, security leaders must understand the threat landscape across both the physical and cyber dimensions.
This means going beyond securing locations and bodies in the real world. Teams must consider their clients' online identities and reputations in the digital realm, too.
The modern security professional has to see the connection between digital privacy and physical safety. And they must be able to educate a principal on the benefits of taking a proactive stance against online threats.
For example, this could include conducting a client assessment of what information a protectee has exposed online.
This requires going beyond a simple Google search. Teams also must consider other places where personal information could be hiding, such as data brokers, chan boards, alt-tech social networks, and the dark web.
They also have to educate clients on how attackers could exploit this information. And where possible, start to proactively remove such data from publication.
In other words, the modern protector can no longer claim “I don’t use Facebook,” or “I only know how to use my phone for calls.” They simply have to be comfortable collecting open-source intelligence from online sources.
Because while some close protection teams may rely on old-school techniques to keep clients safe, the ‘bad guys’ certainly aren’t.
7 Ways OSINT Supports Close Protection
Attackers could have any number of reasons for targeting a protectee – from kidnapping for a ransom to a romantic obsession.
Regardless, open-source intelligence can help teams spot threats, understand attacker motivations, and implement a quick, effective response.
Here are a few examples of how many teams already use OSINT for close protection.
- Violent Threats. Threat actors, surprisingly, often discuss plans to harm or attack their targets publically online. Most of these threats originate from “keyboard warriors.” But in other cases, statements will require further attention. OSINT, however, can alert protectors of a possible attack. In addition, intelligence gathered online also allows protection teams to differentiate between real threats and individuals simply venting their frustrations.
- Doxxings. Doxxing refers to publishing personally identifiable information (PII) online without the subject's permission. For example, this could include facts about a principal such as logins, passwords, email addresses, family members, medical information, banking details, and social insurance number. Individuals publishing this information could have a variety of motives. Regardless, having this data out in the open online exposes a principal to a variety of threats. OSINT allows security teams to potentially uncover such breaches and mitigate these risks as soon as possible.
- Misinformation. Misinformation refers to the unintentional spread of false rumors or reports. For instance, consider a fallacious news report that an executive’s company plans to announce layoffs. Or maybe a conspiracy website has speculated their business has connections to a human trafficking ring. While these reports may have no basis in reality, they could spark public outcry. All of which could expose an executive to very real threats of violence. That’s why protectors need to keep close tabs on what people say about their principal online, whether it’s true or not.
- Travel risk. Protecting an executive on the road starts long before they depart for their trip. Gathering open-sourced intelligence, such as climate, crime rates, civil unrest, terrorist activity, and other factors, allows close protection details to create a travel plan that maximizes safety. Continuous monitoring of open channels also results in a living threat assessment, putting teams in the position to adapt to emerging risks on the fly.
- Data leaks. Social media posts from fans, family members, or the general public can compromise a VIP’s safety. For instance, an executive’s child might publish a post about their upcoming trip on Facebook. Or a fan may upload a photo of the principal visiting a local coffee shop. Such posts could attract unwanted attention from media outlets. Or even worse, such leaks could reveal a VIP’s location to more nefarious individuals.
- Disruptions. Planned disruptions, such as a prank at an event or near a company facility, could result in a public relations nightmare for a high-profile individual. In the worst-case scenario, such incidents could jeopardize their physical safety. Gathering OSINT on any mischief-makers can allow protection teams to take appropriate measures ahead of time.
- Pre-event reconnaissance. Before any public engagement, close protection teams will often conduct pre-event recon. Typically, this process addresses problems like transportation, staffing, venue security, etc. That said, reviewing public sentiment and online chatter leading up to an event can pay dividends. This can tip off protectors to unexpected problems and allow them to adjust plans on the fly.
Where to Uncover Actionable Open Source Intelligence
OSINT refers to gathering intelligence from any free, public source. Technically, this includes mediums like books, newspapers, libraries, etc.
In practice, however, most modern-day OSINT is conducted online. Users upload terabytes of information to social media each day, so analysts collect the bulk of their intelligence on the web.
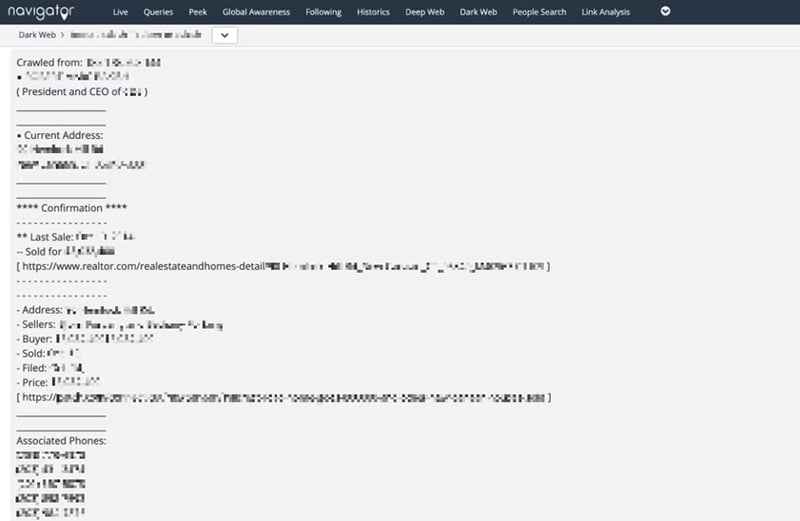 Leaked PII of a senior executive on the darknet, including wi-fi passwords, home address, and family member information, discovered by Navigator.
Leaked PII of a senior executive on the darknet, including wi-fi passwords, home address, and family member information, discovered by Navigator.
Where they look for information depends on what they want to find.
Running a simple Google search amounts to OSINT 101. But in many cases, this might be all a team needs to get the job done.
More often, however, security teams will need to review multiple sources.
This is especially true when conducting passive surveillance or while performing an audit of public information on a client.
Such OSINT sources often include:
- Traditional social networks. Mainstream social networks have the most users. And by extension, they have the most data. For that reason, these sites represent the bulk of most OSINT data collection.
- Alt-tech social networks. Millions of users in recent years have migrated away from the mainstream platforms to a growing collection of alt-tech social networks. Top examples include Telegram, 4Chan, and Gab. While alt-tech social networks are smaller than their mainstream peers, together they have a considerable userbase. So close protection teams that fail to monitor these sites could overlook serious threats.
- Data directories and brokers. Data directories and brokers provide a list of facts on individuals, such as names, addresses, family members, criminal records, and phone numbers. These services often have free rein to buy and sell the personal data of individuals, without even notifying them that they have it. Consequently, any bad actor can use brokers and directories to create a pretty comprehensive picture of their target. And for that reason, protection teams often put out requests to have sensitive information removed from these sites.
- Data breaches. Breached data refers to any stolen or leaked information published online. These data sets often turn up on various paste sites or web forums. And while most consist of only usernames and emails, some can contain more sensitive PII such as banking, medical, and passport information.
- The dark web. The dark web consists of a network of encrypted online content unindexed by traditional search engines. While this part of the internet provides many noble functions, its anonymous nature makes for a perfect place to conduct criminal activities. For that reason, the dark web serves as a popular place to market breached data, unload stolen goods, or plan violent attacks.
The Bottom Line on OSINT for Close Protection
Open-source intelligence is not a silver bullet for every security program.
Obviously, analysts can only detect potential threats from public information. If a bad actor conceals their activities, they can be difficult to detect.
Additionally, protectors that start applying OSINT can suffer from information overload. And it can be tough to separate valid, verified information from fake news and reports.
Yet, despite these limitations, OSINT still represents a dramatic force multiplier for short-staffed security teams.
It’s far easier to proactively address a threat rather than respond to an incident after the fact. OSINT allows close protection teams to address the growing number of risks to a principal in the cyber realm as well.
All of which can go a long way toward keeping an executive, celebrity, or other VIPs safe.